OAIC Data Breach Report: July – December 2022
Key Findings in the OAIC’s Data Breach Report: July – December 2022
The OAIC highlighted the following key findings in its July – December 2022 Data Breach Report:
- There was a 26% increase in breaches.
- There was a 41% increase in malicious or criminal attacks.
- There was a 67% increase in large-scale data breaches.
- There were fewer data breaches caused by human error (down 5% from January to June 2022).
- Data breaches caused by a system fault tend to take longer to identify.
Key Takeaways from the OAIC’s Data Breach Report: July – December 2022
Cyber Security Risk in Australia is Increasing
Almost half (45%) of the data breaches between July – December 2022 resulted from cyber security incidents. They were also the cause of most of the large-scale breaches we saw during this period.
The most common causes of breaches resulting from malicious or criminal attacks are:
- Cyber incidents
- Social engineering/impersonation
- Theft of paperwork or data storage device
- Rogue employee/insider threat.
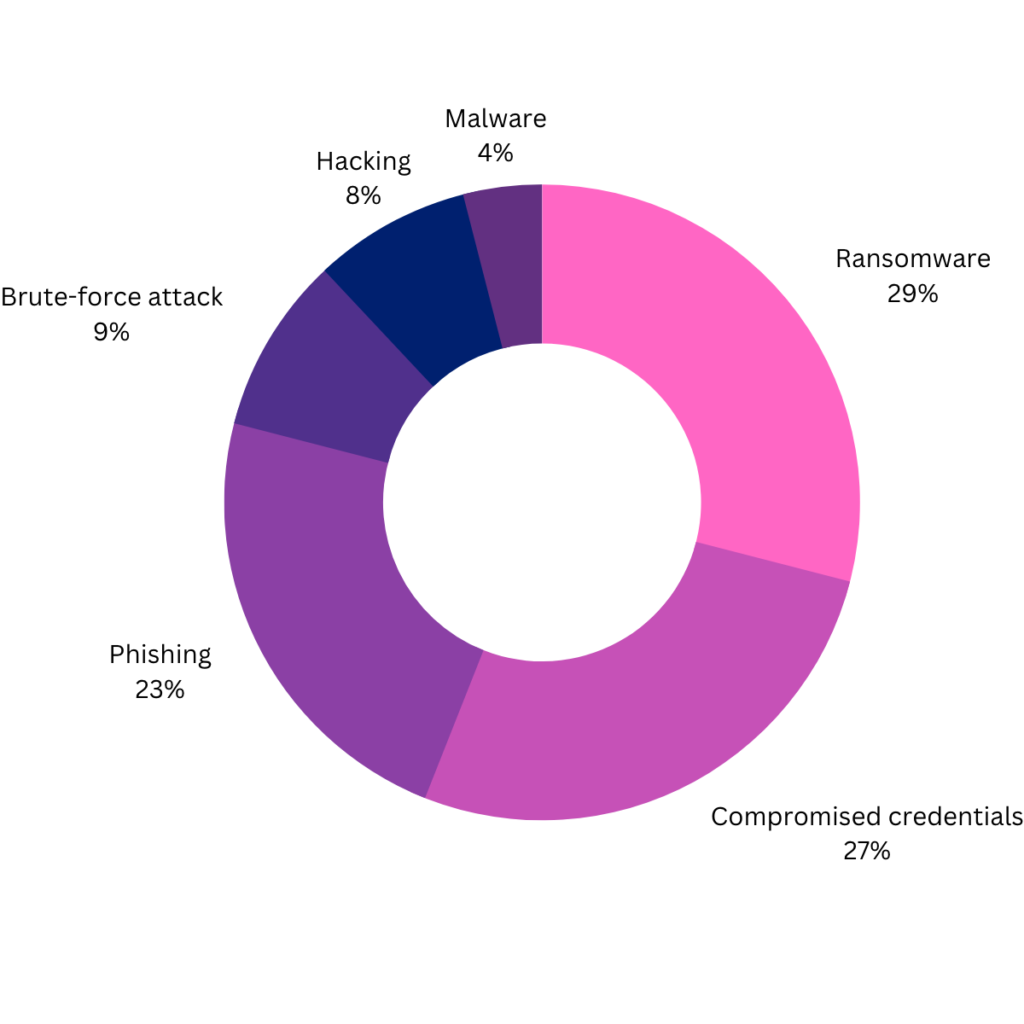
Digging deeper into the source of cyber incidents, the OAIC revealed the most common causes of cyber incidents:
- Ransomware
- Compromised or stolen credentials (method unknown)
- Phishing (compromised credentials)
- Brute-force attack (compromised credentials)
- Hacking
- Malware.
One Quick Tip for Managing Your Cyber Security Risk
One of the most effective ways to manage your organisational cyber security risk is to collect the minimum amount of information and to ensure it is deleted when it is no longer required.
Large-Scale Breaches Are Increasing, Too
The Optus and Medibank breaches together impacted tens of millions of Australians. However, these were not the only large data breaches that were notified between July – December 2022. There was actually 67% increase in the number of breaches that impacted 5,000 or more Australians during this period.
It’s worth noting that there was also an increase in the number of large-scale breaches in the January – June 2022 period. If we look at the figures on a year-over-year basis, there has been a 100% increase in large-scale data breaches since 2021.
| Number of Australians affected by breaches | Jul-Dec 2021 | Jul–Dec 2022 |
| 5,001–10,000 | 8 | 12 |
| 10,001–25,000 | 7 | 8 |
| 25,001–50,000 | 2 | 6 |
| 50,001–100,000 | 2 | 4 |
| 100,001–250,000 | 0 | 2 |
| 250,001–500,000 | 0 | 2 |
| 500,001–1,000,000 | 0 | 1 |
| 1,000,001–10,000,000 | 1 | 5 |
| 10,000,000+ | 0 | 1 |
| Total number of breaches affecting over 5,000 Australians | 20 | 40 |
Timely Notifications More Important Than Ever
We all noted the reputational harm that came from Optus’ slow and poor communications about the large-scale data breach. However, as both the incidence of breaches and the sensitivity of the data being breached increase, timely notifications are expected by individuals – as well as the OAIC.
The OAIC was given increased powers under the Privacy Legislation Amendment (Enforcement and Other Measures) Bill in 2022 – including a new power to obtain information and documents relevant to an actual or suspected eligible breach. The OAIC may now enforce significantly higher penalties for serious breaches, too. So, from a regulatory risk perspective, Australian organisations now have a greater incentive to identify breaches and engage in timely notifications.
System Fault Breaches and Timely Notifications
It’s worth noting that system fault breaches are generally detected more slowly than human error breaches or malicious/criminal attacks. In fact, one-third of system fault breaches were not identified for over one year (compared to 3% for malicious/criminal attacks and 4% for human error breaches).
Organisations should conduct a privacy impact assessment and an information security risk assessment to reduce the risk in this regard. It’s also important to implement technical measures to monitor and detect these breaches.
Third-Party Vendor Breaches: One to Watch
When more than one entity holds personal information that is breached, all the entities that hold the information have obligations under Australia’s Notifiable Data Breach scheme. And the number of organisations being affected by third-party vendor breaches is increasing.
There was a 91% increase in secondary notifications in July – December 2022.
Quick Tips for Managing Third-Party Privacy Risk
We discussed third-party risk in a detailed blog post, but some quick takeaways are:
- Ensure your contract contemplates your joint data breach response.
- Implement access control and only allow third parties access to the personal information they need to achieve their purposes – no more.
- Ensure your privacy policy provides accurate details about which third parties you share data with and what agreements govern those relationships, as well as what privacy measures are in place.
Data Breach Management with Privacy 108
Our data breach management services include:
- Developing an information security incident response capability;
- Preparing a data breach response plan;
- Testing and training staff in your incident response;
- Participating as legal advisers and/or privacy experts as part of your data breach/incident response team;
- Keeping you up to date with new or changing data breach notification obligations;
- Providing a legal opinion on your data breach notification obligations; and
- Participating in or leading the post-incident review process.
For assistance managing and securing your organisation’s data, reach out. Our privacy team would love to assist.